Teen hackers — flash of genius or a serious threat?
Good skills, bad execution
Some time ago, there was a buzz about a 16-year-old from Plympton, Devon, who started hacking websites of organizations and governments at the age of 14. Not only did he hack into government networks, but he also sent bomb threats to US airlines. The 14-year-old boy used a laptop to cause mayhem in Iraq’s foreign ministry from the comfort of his room. The fun ended when the teen was arrested after sending fake bomb messages to American Airlines, Delta Airlines and the White House.
Online security — what do hackers actually do?
Hackers engage in activities that are designed to break into digital systems. While not all hacking is done for a malicious purpose, these days most often “hacking” simply means cybercrime. Usually motivated by financial gain, protest, spying, or “just plain” fun.
Hacking is usually some kind of technique. It can involve, for example, the creation of malware that introduces malicious code without the user having to interact with the system in question. However, sometimes hackers also use psychological tricks. They do this to persuade a computer user to click on a malicious attachment or to provide personal information (known as social engineering).

Data security: how do hackers “play”?
In the past, hacking boiled down to remotely setting pink wallpaper on a friend’s computer for a prank. With the passage of time and advances in technology, hacking has evolved from a youthful prank to a multi-billion dollar business. In addition to malicious advertising and social engineering, typical hacker attacks consist of:
- Taking control over browsers
- Botnets
- Distributed denial of service attacks (DDoS)
- Ransomware
- Rootkits
- Trojans
- Viruses
- Warms
Online security is so important today because youthful pranks have turned into an entire criminal infrastructure. This one is constantly evolving, and on top of that, it sells hacking tools for would-be scammers who are a little less tech-savvy (script kiddies).
Online security — from a hacked journal to cyberbullying
Talented teenagers choose to go into hacking for various reasons. It does not necessarily have to be about hacking into government networks or servers of major brands. Very often the consequences for the outside world are much smaller than for the child.
As an example can be used the fate of a student from the Wielkopolska region, who broke into the IT system of his school and changed the grades of his classmates. First, he used a replica of the website, then he used the appropriate script and sent a link to the website, all in order to obtain the password of one of the teachers in the final stage. In this way, he gained full access to the electronic journal. The school management assures that the data stored in the systems are secure, and the incident is explained by the teenager’s great skills.
Hacking into the school logbook is one of many threats. Another threat worth keeping in mind is cyber aggression (heckling, cyberbullying). It is important to pay attention not only to the behavior of other users toward our children, but also to how our children behave online. A child can be held legally responsible not only for hacking systems, but also for bullying and harassing other online users. Cyberbullying on social media is a vast topic, so it deserves our attention all the more.
Support interests before they grow into hackers
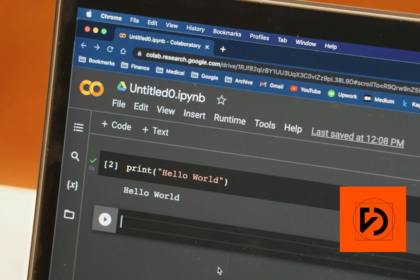
Have control over how your child uses the computer. It’s not only about eliminating the danger by imposing various types of blockades, but above all about directing your child’s interests accordingly. The computer, despite its numerous dangers, is not your enemy. If your child shows interest in programming, it does not mean that he or she will join the ranks of hackers. These skills can be used differently. If they go the wrong way, they should not be suppressed, but put back on the right track.
New technologies are developing new branches of services and opportunities for future jobs. New information, new security requirements, or different types of content are constantly arriving. The ability to creatively use the Internet, acquire data and handle it efficiently, not only streamlines work, but also opens up opportunities to create new solutions and technologies. If you combine it with the ability to program and think logically, you can create your own profession. Therefore, we should not treat technology as a threat. Instead, it is better to look at it as an opportunity for multidimensional development. Most of today’s children, in the future, will work in professions that do not exist today.
Teen hackers — the consequences of the fun
The biggest consequence faced by teenage hackers is not the prospect of jail time. For children and adolescents entering the path of crime, the worst are the psychological traumas. This includes depression, as well as the difficulty of coping with their hacking “accomplishments” and finding their way back into normal life. Theft and fraud on the Internet, is no less real than it is in offline life. You can find this out when someone steals your card information and drains your bank account. The fact that the theft took place in the virtual world does not diminish its impact in the outside world.
A teenage hacker usually does not think about the consequences of his actions, but about having fun and finding recognition among his friends. The child is very often looking for acceptance by taking up activities related to cybercrime. Therefore, it is necessary to take care of his/her self-esteem, properly understood purpose, show possibilities, thanks to which he/she will be able to fully develop their competences without entering the path of crime.
Startups as the answer to great skills
Nowadays, the founders of startups are often above-average teenagers. For them, the computer and the Internet have no secrets. Although there are dangers present on the web, such people are able to use technology in a creative way. Not to do harm, but to provide a variety of solutions which are supposed to make life easier and give some value to their users.
At Da Vinci Studio we value interesting startups and young talent. We help to direct skills and provide important information. We are happy to share our knowledge and experience. Contact us to learn about the specifics of our work and, most importantly, to spread your talented child’s wings.